LDAP as Identity Source
# Overview
IDaaS supports various third-party systems as identity sources, and also supports using an enterprise's internal LDAP directory as an identity source for IDaaS. It synchronizes with the organizational structure and user information in the LDAP to achieve unified data management and data consistency.
# Prerequisites
- The IDaaS public cloud service can access the LDAP directory service. If network policies exist for the LDAP server, you can add the IDaaS public cloud service IP (47.92.171.137) to the network whitelist.
- Have administrator permissions for the IDaaS Enterprise Center platform.
# Steps
Log in to the IDaaS Enterprise Center platform. In the top navigation bar, select "Users > Identity Source Management", click "Add Identity Source" and choose the "LDAP" identity source.

Customize the identity source name, fill in parameters such as Host, TCP Port according to the interface prompts. After setting, click "OK" to save.
Enter the details page of the newly added identity source. You can view and update the "Basic Configuration" of the LDAP identity source, including connection parameters and synchronization mechanisms.

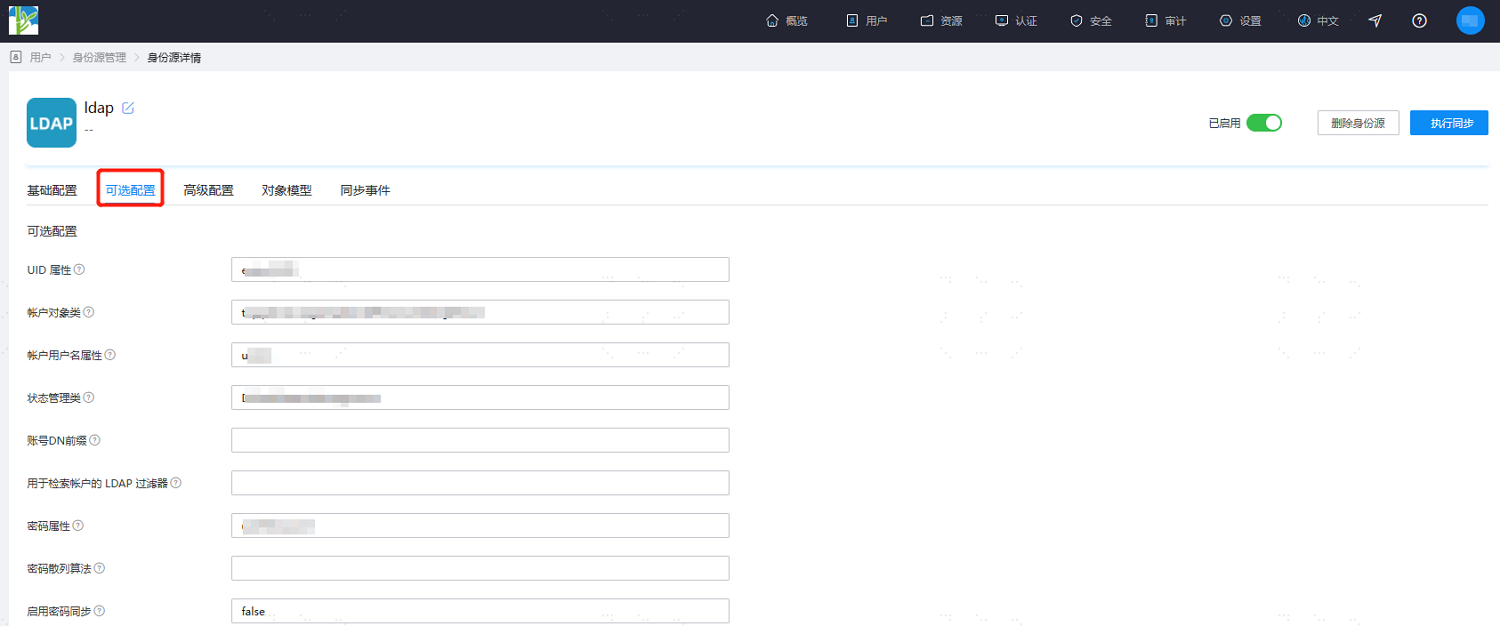
Switch to the "Optional Configuration" tab. It is recommended to keep the defaults or fill in according to the interface based on actual needs.
After configuration, switch to the "Advanced Configuration" tab. It is recommended to keep the defaults or fill in according to the interface based on actual needs.
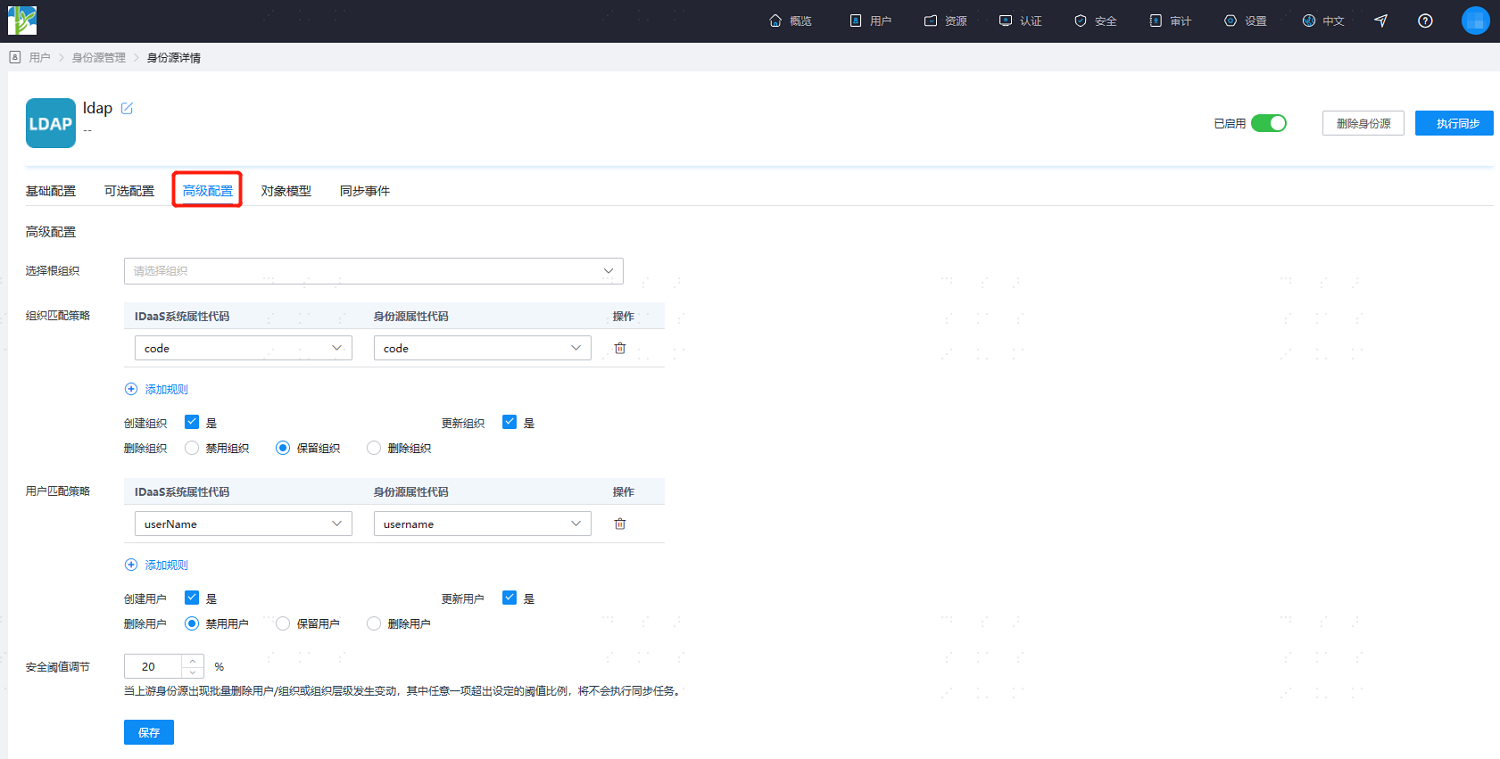
Parameter Description Select Root Org The location of the organizational node synchronized into IDaaS Org Match Policy Organizations can be matched by mapping attribute names in IDaaS with those in the LDAP identity source. Supports adding multiple matching rules, e.g., matching LDAP directory organizational code with IDaaS organizational code. Create Org Default is Yes Update Org Default is Yes Delete Org Sets how IDaaS handles an organization when it is deleted in LDAP. Supports disabling, retaining, or deleting the organization. User Match Policy Users can be matched by mapping attribute names in IDaaS with those in the LDAP identity source. Supports adding multiple matching rules, e.g., matching unique user attributes from the LDAP directory with unique user attributes in IDaaS. Create User Default is Yes Update User Default is Yes Delete User Default is to disable the user (i.e., when a user is deleted in LDAP, the user is disabled in IDaaS). Also supports retaining or deleting the user. Security Threshold Adjustment Sets the maximum threshold percentage for changes such as deleting users/organizations or organizational hierarchy changes when they occur in the upstream identity source.
Threshold = (Difference between data already reclaimed by the platform and this batch of reclaimed data / Already reclaimed data) * 100%. When the upstream identity source disables/deletes data exceeding the set threshold, the platform will not perform the disable/delete operation upon receiving the instruction.After configuration, switch to the "Object Model" tab and select "Mapping Definition". Complete the attribute definition and mapping definition based on actual needs. Key parameter descriptions are as follows.
The object model supports mapping attributes from users and organizations in the LDAP identity source to attributes of users and organizations in IDaaS. After setting, it enables reclaiming user and organizational attributes from LDAP to IDaaS user and organizational attributes.
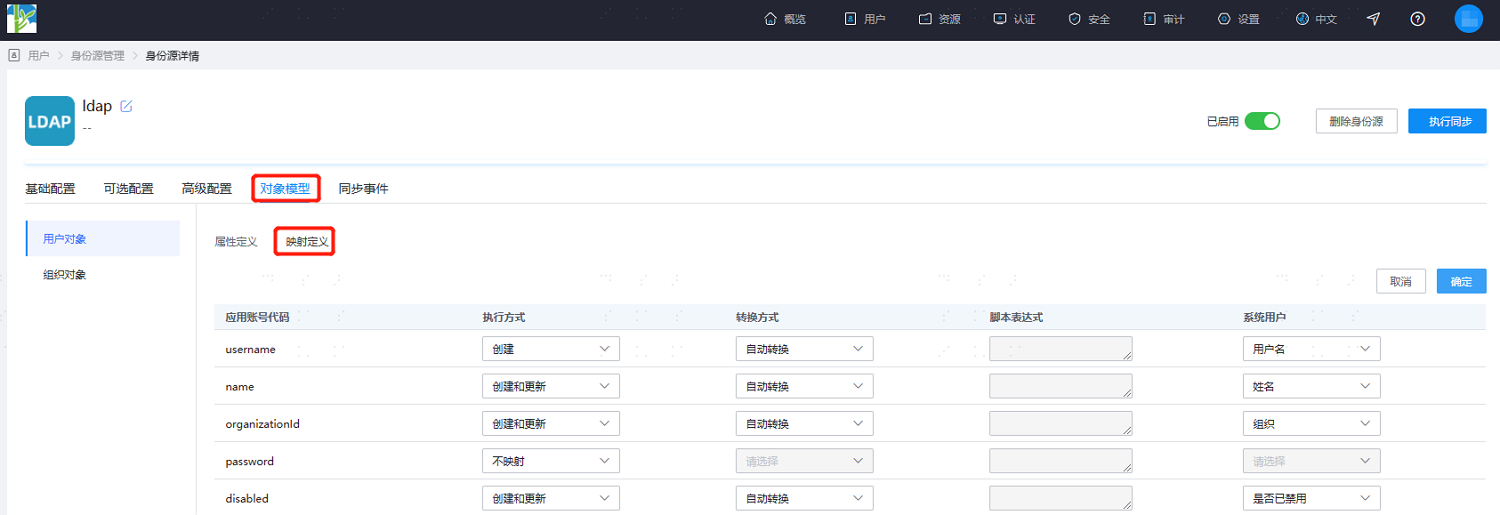
- Execution Method: Sets under which circumstances the attribute needs to be mapped.
- Do Not Map: This attribute will not be synchronized to IDaaS.
- Create: This attribute is synchronized only during creation.
- Update: This attribute is synchronized only during updates.
- Create and Update: This attribute is synchronized during both creation and updates.
- Conversion Method: Sets the method for attribute mapping.
- Auto Convert: Synchronizes whatever value is in the identity source.
- Script Convert: If the value from the identity source does not meet the required format, this method can be used for conversion. Please refer to Script Mapping Method.
- Execution Method: Sets under which circumstances the attribute needs to be mapped.
After completing the object model setup, click "Execute Sync" to immediately perform the synchronization operation.
If the synchronization mechanism in the basic configuration is set to scheduled sync, manual execution of the sync task is not required here.
After execution is complete, switch to the "Sync Events" page to view all synchronization tasks for this identity source. Click "Details" under the "Actions" column to view the import results, or go to the "Users > Users & Organizations" page to view the imported data.
