Configure OIDC Authentication Source
# Overview
To facilitate enterprise user authentication and login, the IDaaS platform supports configuring the OIDC protocol as an authentication source. Users can authenticate and log in to various application systems via the OIDC protocol, providing enterprise users with a simpler, more convenient login method and a better user experience.
This chapter introduces the related operations for configuring an OIDC authentication source.
# Prerequisites
- Possess administrative permissions for the application system of a third-party identity provider (IDP), and that identity provider must support OIDC authentication.
- Possess administrator permissions for the IDaaS Enterprise Center platform.
# Steps
# Third-party OIDC Authentication Platform Configuration
- Create an application on the third-party platform with OIDC as the access method, and complete the relevant application information. For detailed operations, please refer to the respective platform's documentation.
- Grant users access permissions to the newly created application.
# IDaaS Platform Configuration for OIDC Authentication Source
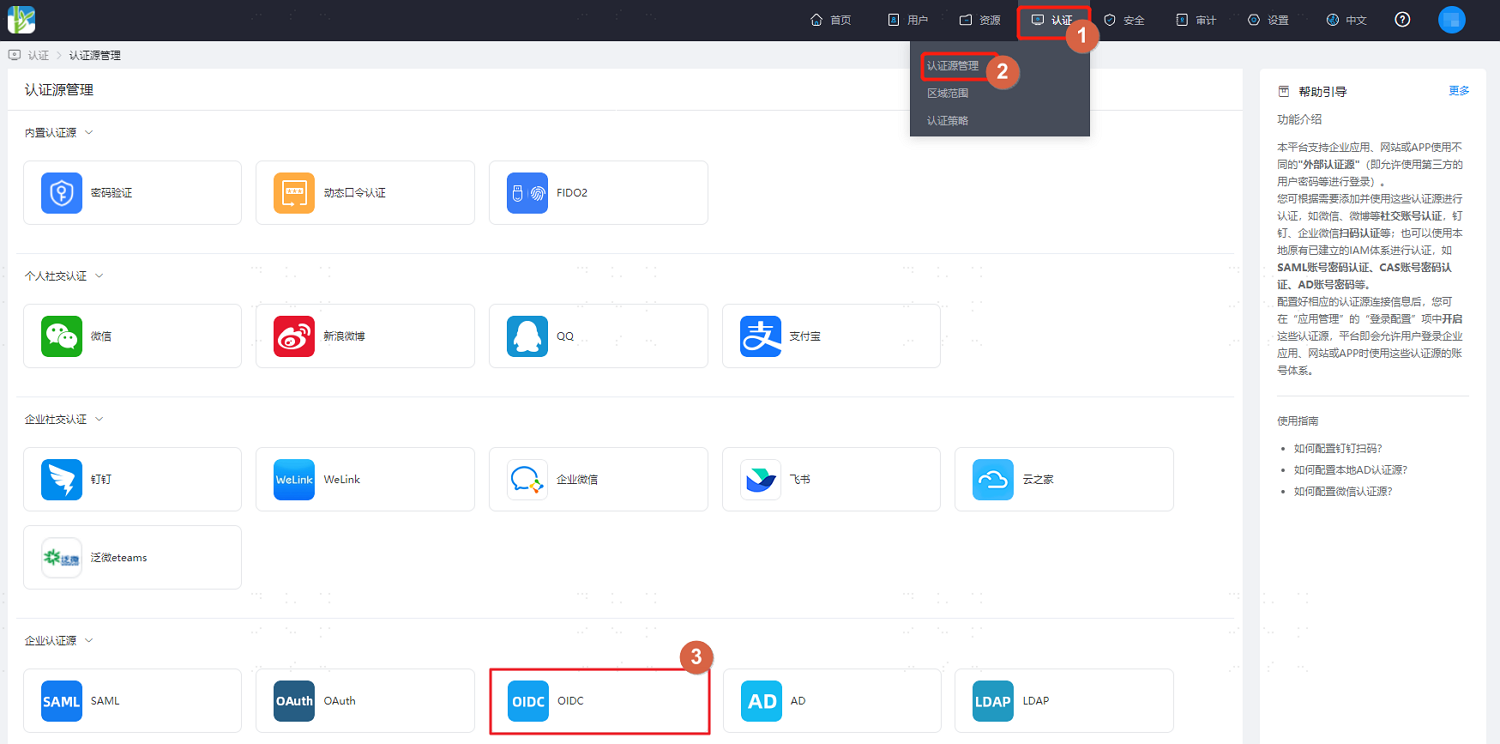
- Log in to the IDaaS Enterprise Center platform. In the top navigation bar, select "Authentication > Authentication Source Management," go to the OIDC authentication source page, and click "Add Authentication Source."
- Configure the OIDC authentication source parameters according to the interface prompts. Key parameter descriptions are as follows.
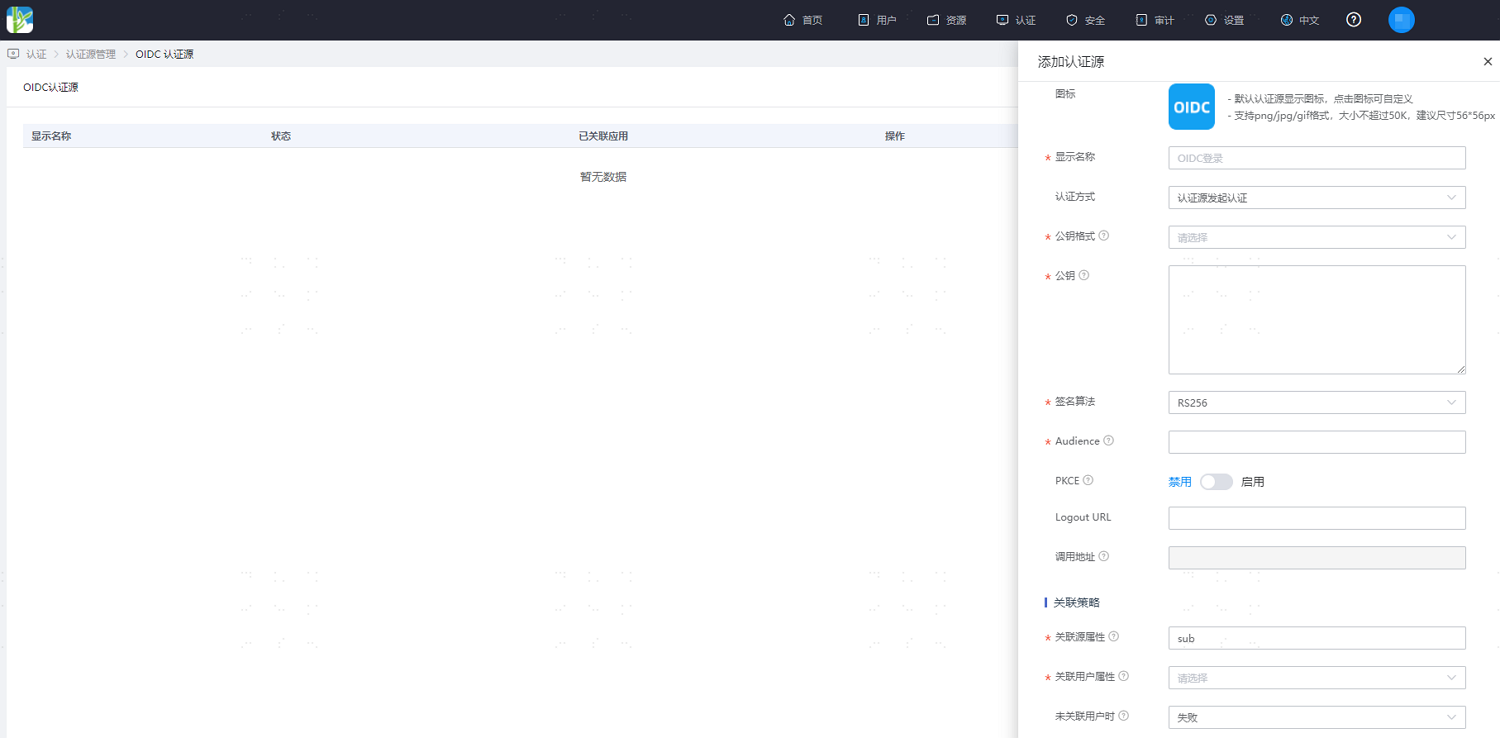
| Parameter | Description |
|---|---|
| Public Key | Obtained from the OIDC jwks_uri or provided by the authentication source administrator, matching the public key format.When the public key format is JWKURL, the public key is https://{Okta domain}/oauth2/v1/keys.When the public key format is JSON format public key, the public key is the value from https://{Okta domain}/oauth2/v1/keys. |
| Flow Type | This configuration appears when the authentication method is set to "Initiate Authentication Actively." Select the corresponding flow type based on the application configuration, such as Authorization Code mode, from the dropdown menu. |
| response Type | Optional configuration, and only appears when the authentication method is set to "Initiate Authentication Actively." Default is code. |
| scope | Appears when the authentication method is set to "Initiate Authentication Actively." Corresponds to the scopes configuration on the OIDC authentication source side. Must include "openid", e.g., openid email. |
| authrozationUrl | Appears when the authentication method is set to "Initiate Authentication Actively." Corresponds to the value of "authorization_endpoint" on the OIDC authentication source side. |
| clientld | Appears when the authentication method is set to "Initiate Authentication Actively." Corresponds to the value of "Client ID" on the OIDC authentication source side. |
| Audience | Appears when the authentication method is set to "Authentication Source Initiates Authentication." This field parameter is included when obtaining configuration from the OIDC application side. |
| LogoutUrl | Optional configuration. The global logout URL for the application, obtained from the application side. |
| Callback URL | Generated by the system by default. Corresponds to the Login redirect URIs parameter of the application. |
| Source Attribute | The unique attribute of the user on the OIDC authentication source side. E.g., email. |
| Associated User Attribute | The mapping attribute for connecting the OIDC authentication source to IDaaS. E.g., Email, selectable from the dropdown menu. |
| When User Not Associated | When a user successfully logs in using the OIDC authentication source but is not associated with a system user, operations can be performed according to this setting, such as automatically creating a user, selectable from the dropdown menu. |
When User Not Associated: This refers to when the user information returned by the third-party platform (the Source Attribute) does not match the Associated User Attribute in IDaaS, resulting in no association to a system user. The optional configuration items are as follows.
Fail: Set to "Fail," meaning this user is not allowed to pass authentication.
Automatically Create User: Set to "Automatically Create User." You can choose whether to update existing attributes. Simultaneously, click "Add Mapping" to map user attributes from the third-party platform to IDaaS user attributes based on mapping rules and associated attributes, creating the user and allowing them to pass authentication.
Attribute descriptions are as follows:
- User Attribute Name: Select the user attribute in IDaaS from the dropdown.
- Mapping Type: Select Authentication Source Attribute.
- Authentication Source Attribute Name: The user attribute from the third-party platform.
