Authentication Source Cloud Bridge
# Overview
The Authentication Source type Cloud Bridge is a type of IDaaS Cloud Bridge used to establish a connection channel between Zhuyun IDaaS and the corresponding authentication source within the enterprise. It currently supports two types of authentication sources: AD authentication source and LDAP authentication source.
This section guides you through deploying and using the Authentication Source Cloud Bridge Agent on the IDaaS platform and provides update records for the Authentication Source Cloud Bridge installation package, so you can choose the appropriate version based on your project's actual needs. The following uses the operating system CentOS Linux release 8.0.1905 to deploy the Authentication Source Cloud Bridge Agent as an example.
# Prerequisites
Have administrator permissions for the IDaaS Enterprise Center platform.
Have operational permissions for the intranet server.
The server has net-tools, curl, jdk (OpenJDK 17 or higher), and rng-tools installed. Installation steps are as follows:
net-tools installation
- Verify if net-tools is already installed
rpm -q net-tools1 - If not installed, download (opens new window) the installation package and upload it to the intranet server.
- Navigate to the directory containing the file and execute the installation command.
yum -y install net-tools-2.0-0.22.20131004git.el7.x86_64.rpm1 - Verify the installation.
rpm -q net-tools1
curl installation
- Most Linux distributions come with curl pre-installed; simply verify its installation.
curl --version1
jdk installation
- Download (opens new window) the installation package and upload it to the intranet server.
- Navigate to the directory containing the file and execute the installation command.
yum -y install jdk-17.0.13_linux-x64_bin.rpm1 - Verify the installation.
java -version1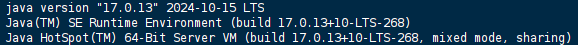
rng-tools installation
- The rng-tools tool needs to be installed to increase the replenishment rate of the system entropy pool. Execute the following command to install rng-tools:
yum install rng-tools1 - Check if the rngd configuration file exists:
cat /etc/sysconfig/rngd1 - If the file does not exist or its content is empty, execute the following command to create the file:
echo "OPTIONS=\"-r /dev/urandom\"" > /etc/sysconfig/rngd1 - Execute the following commands to start the rng service and check its status.A status of enabled indicates a successful start:
service rngd start Start the rng service service rngd status Check the rng service status1
2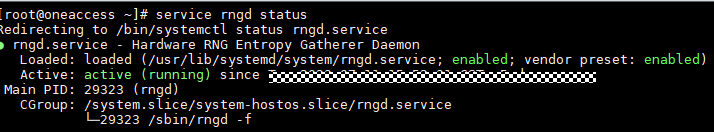
- Verify if net-tools is already installed
# Pre-deployment Preparation
# Software Packages
Please prepare the software packages as shown below in advance.
| Package Name | Description | Download Link |
|---|---|---|
| cloudAgent-authSource-{version}.zip | Authentication Source Cloud Bridge installation package. | Download Here (opens new window) |
| cloudAgent-authSource-{version}.zip.sha256 | SHA256 checksum file for the Authentication Source Cloud Bridge installation package, used to verify the integrity of the installation package. | Download Here (opens new window) |
The files after extracting the Authentication Source Cloud Bridge installation package are as follows:
| Name | Description |
|---|---|
| agent.sh | File for auto-starting the Cloud Bridge Agent on boot. |
| cloudAgent-authSource.jar | Deployment package for the Authentication Source Cloud Bridge Agent. |
| cloudBridge.sh | File for manually starting the Cloud Bridge Agent. |
| config | Directory for storing the Cloud Bridge Agent configuration file (application.yml). |
| log | Directory for storing the Cloud Bridge Agent logs (agent.log). |
# Deploy the Authentication Source Cloud Bridge
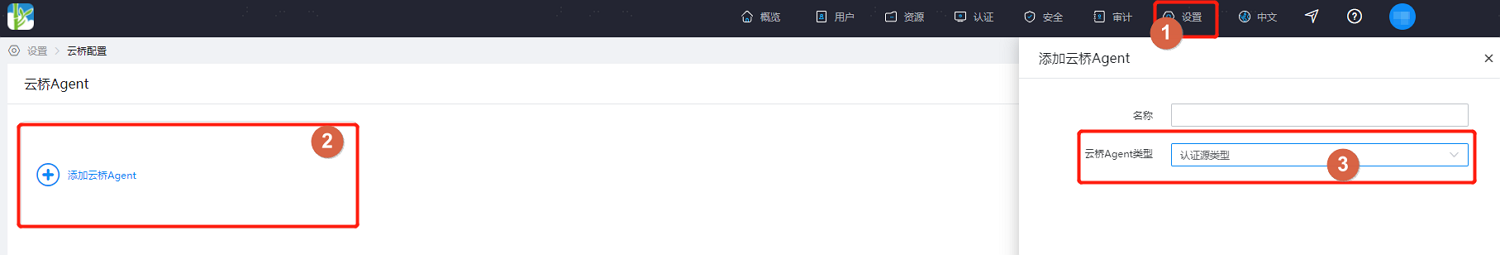
Log in to the IDaaS Enterprise Center platform, select "Settings > Cloud Bridge Configuration" from the top navigation bar, click "Add Cloud Bridge Agent", set a name and select the Authentication Source type Cloud Bridge.
- After the Cloud Bridge Agent is added, the system will automatically generate a ClientID and ClientSecret. Please keep them safe.
- If you forget the ClientSecret, click "Reset Secret Key" for the target Agent to regenerate it. After resetting, the original key will become invalid. Please operate with caution.
- Supports viewing Cloud Bridge connection logs and service logs.
- Supports configuring an IP for the Cloud Bridge Agent. Configure it as the egress IP of the server where the Cloud Bridge Agent is deployed. After configuration, only this IP is allowed to connect to the IDaaS cloud service to ensure service security.
- Supports deleting the target Agent. Please operate with caution.
Upload all the obtained software packages for the Authentication Source Cloud Bridge to the target server. Execute the following command to verify the integrity of the Cloud Bridge installation package. When the echoed information shows OK, it indicates successful integrity verification.
sha256sum -c cloudAgent-authSource-{version}.zip.sha2561Execute the following command to extract the Authentication Source Cloud Bridge installation package. The storage location must be unique; otherwise, it will cause installation errors.
unzip -od {storage location for extracted files} cloudAgent-authSource-{version}.zip1Navigate to the directory where the files were extracted and configure the
application.ymlfile in the config directory.###UTF-8 format YAML configuration header, do not delete### server: # Cloud Bridge startup port port: 9082 agent: # Cloud Bridge service address, domain is the tenant domain in IDaaS xx.bccastle.com Example: serverAddress: wss://domain/api/v1/ws # Cloud Bridge ClientID, the ClientID of the Cloud Bridge created in IDaaS Example: agentId: 7jve68NwihfnjsD8SJToWxTU5Wg8hkl1 # Cloud Bridge ClientSecret, the ClientSecret of the Cloud Bridge created in IDaaS Example: agentSecret: LdfwryojYHLMaeNGVdr9fSh1iwyDCL0QuBx2wewrjxT5UOhUQVpAqwerfgj8pLNV1 authentication: ad: # AD authentication switch, default value is false, set to true to enable AD authentication Example: enable: false # AD server address, format is ldap://host:port/, use , to separate multiple addresses. When there are multiple addresses, the schema must be the same for all, either all ldap or all ldaps. Example: urls: ldap://localhost:389/ # Node in AD, users will be queried under this node. Example: rootDn: User # Domain in AD. When a domain exists, the login name + @ + domain is automatically concatenated as the query condition; otherwise, only the login name is used as the query condition. Example: domain: test.ad.com # User query condition, searches based on object class and user login name; userPrincipalName can be adjusted according to the actual situation; # Placeholder explanation: {0}-query with domain, page input value + domain, e.g., zhangsan@companya.cn, # When no domain is present, the domain attribute value from the authentication source is concatenated and then queried. {1}-query with original value, using the page input value for query, e.g., zhangsan. Example: searchFilter: '(&(objectClass=user)(userPrincipalName={0}))' # AD connection timeout, configurable range 1000 - 3000 milliseconds Example: timeout: 10001
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29ldap: # LDAP authentication switch, default value is false, set to true to enable LDAP authentication Example: enable: false # LDAP server address, format is ldap://host:port/, separate multiple addresses with , (comma). When using multiple addresses, the schema must be the same for all, either all ldap or all ldaps Example: urls: ldap://localhost:389/ # The top-level root directory of the LDAP directory tree Example: baseDn: DC=test,DC=com,DC=cn # LDAP administrator account identifier Example: managerDn: testadmin # LDAP administrator account password Example: managerPassword: Passw0rd # Ldap common search path Example: userSearchBase: ou=people # Filter condition for matching system users in LDAP. For details, please refer to: https://ldap.com/ldap-filters/. Query based on conditions has lower priority than query based on DN. Example: userSearchFilter: (&(objectClass=user)(uid={0})) # Fill in the user ID or organizational unit. Ldap user search path, excluding BaseDn. User DN pattern query takes priority. Example: dnPatterns: uid={0},ou=people # LDAP connection timeout, configurable range 1000 - 3000 milliseconds Example: timeout: 1000
# This is the Agent log level control configuration
logging: level: com.bamboocloud.bcidaas.cloudbridge: DEBUG file: # The value of the attribute must have a unit, which can be KB or MB # Single log file size. Default value 10MB, maximum value 10MB # default: 10MB # max-size: 10MB # The maximum number of days that log files are to be archived # Maximum log retention time. Default value 7 days, maximum value 7 days # default: 7 DAYS # max-history: 7
1After completing the configuration file, execute the following command in the directory where the Cloud Bridge installation package is extracted to start Cloud Bridge. When prompted with Starting Agent Success, it indicates that Cloud Bridge has started successfully. If startup fails, please troubleshoot the configuration file.
./cloudBridge.sh start1
(Optional) If you need Cloud Bridge to start automatically on system boot, please execute the following command in the directory where the Cloud Bridge installation package is extracted. When prompted with The Agent service installed successfully, need to reboot will take effect, it indicates successful setup.
./agent.sh install1(Optional) If you need to cancel Cloud Bridge's automatic startup on system boot, please execute the following command in the directory where the Cloud Bridge installation package is extracted. When prompted with uninstall Agent Success, it indicates successful cancellation of Cloud Bridge's automatic startup.
./agent.sh uninstall1You can obtain log information from the
log/agent.logfile in the directory.
# Using Authentication Source Cloud Bridge
- When configuring an AD authentication source on the IDaaS platform to use the Authentication Source Cloud Bridge, please refer to Configuring AD Authentication Source.
- When configuring an LDAP authentication source on the IDaaS platform to use the Authentication Source Cloud Bridge, please refer to Configuring LDAP Authentication Source.
# Update Log
This module displays the update records for the Authentication Source Cloud Bridge Agent installation package.
| Version | Update Description |
|---|---|
| V25.2.1.1 | Upgraded third-party components, fixed security vulnerabilities. |
| V25.2.1.0 | Upgraded Spring version, fixed security vulnerabilities. |
| V24.11.1.0 | Upgraded third-party components, fixed security vulnerabilities. |
| V24.8.2.0 | Security hardening for Cloud Bridge client. |
| V24.4.1.0 | Security hardening for Cloud Bridge client. |
| V24.2.1.0 | Support for configuring AD, LDAP connection timeout. |
| V23.10.1.0 | JDK version upgraded to JDK 17. |
| V23.5.1.0 | Added client connection information and log backup. |
| V22.11.1.0 | 1. Optimized some known bugs. 2. Optimized WebSocket connection. |
| V22.9.1.0 | 1. Modified Cloud Bridge installation script to install watchdog via systemd, supporting Ubuntu system. 2. Installation script added pre-installation environment checks. |
| V22.7.1.0 | Support for viewing Cloud Bridge service logs. |
| V22.6.1.0 | Support for LDAP authentication. |
| V21.10.2.0 | 1. More precise error configuration prompts. 2. Optimized the method for Agent to obtain Pid. |
| V21.9.2.0 | Added watchdog mechanism. |
| V21.9.1.0 | 1. Optimized Cloud Bridge reconnection mechanism. 2. Optimized some known BUGs. |
Understood. I am ready. Please provide the Markdown content you need translated.
