Login Flow
PKCE (Proof Key for Code Exchange) is a cryptographic method that ensures even if a malicious third party intercepts the Authorization Code, they cannot exchange it for an Access Token with the authentication server. It also eliminates the need to store the Client Secret on the client side, preventing the Client Secret from being leaked. This mode is primarily used for clients to obtain user information.
# Login Flow
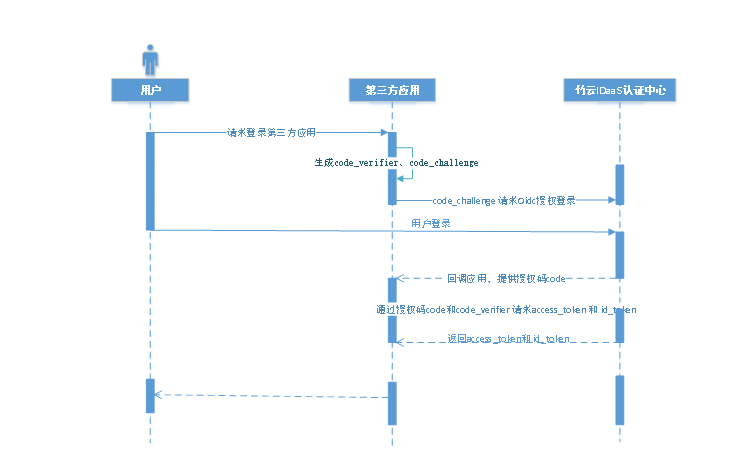
The overall flow using the PKCE mode is as follows:
The user accesses the third-party application. The third-party application randomly generates a string of 43-128 characters, performs URL-Safe Base64 encoding on it, and uses the result as the code_verifier. This string is then hashed using SHA256 and encoded with URL-Safe Base64, and the result is used as the code_challenge.
The third-party application uses the code_challenge to initiate an authorization login request to Zhuyun IDaaS. After the user authorizes the third-party application, Zhuyun IDaaS will redirect back to the third-party application, including the authorization code parameter.
The third-party application uses the authorization code and the code_verifier to call the Zhuyun IDaaS API interface to exchange for an access_token and an id_token.
The third-party application verifies the signature of the id_token, parses the id token, and obtains the user information.
# Development Steps
The Zhuyun IDaaS platform adopts the OIDC PKCE protocol authorization code mode. The access development process is as follows:
# Step1: Obtain PKCE Authorization Code
Click to view the interface for obtaining the PKCE authorization code
# Step2: Obtain PKCE Access Token
Click to view the interface for obtaining the PKCE Access Token
# Step3: Parse ID Token to Obtain User Information
Click to view, obtain user information
