Login Flow
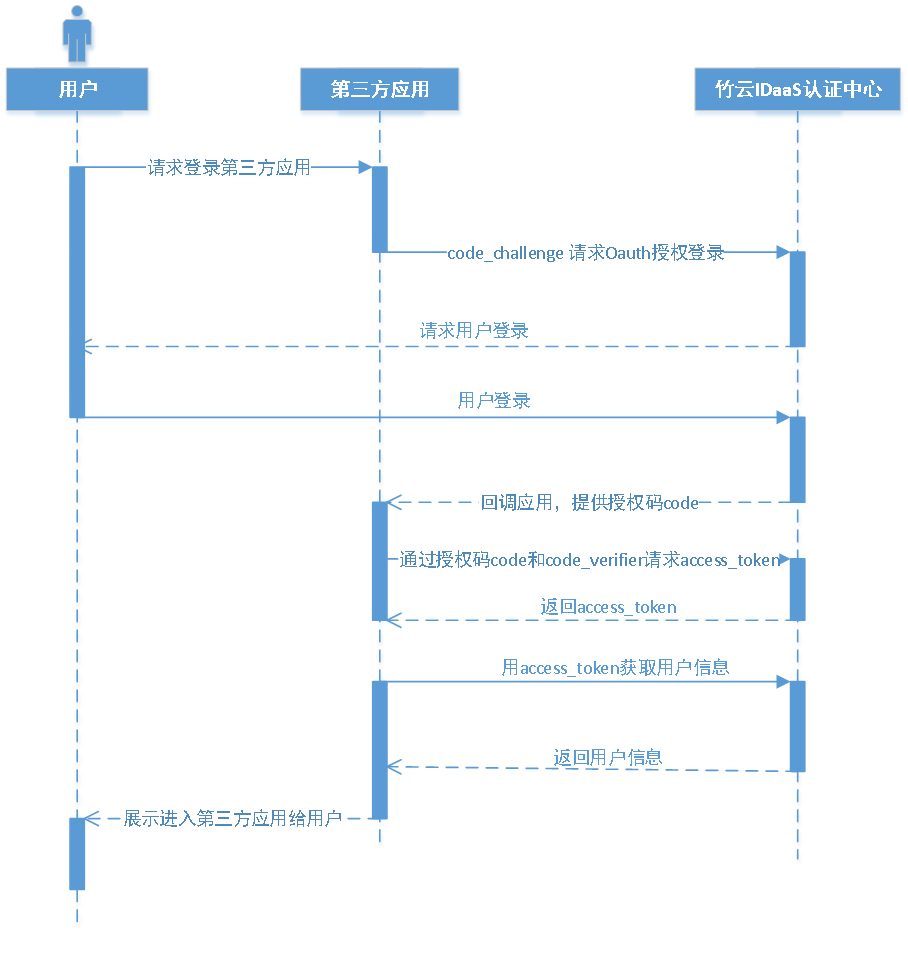
The overall flow using PKCE mode is:
The user accesses the third-party application. The third-party application randomly generates a string of 43-128 characters, performs URL-Safe Base64 encoding on it, and uses the result as the code_verifier. It then hashes this string using SHA256 and performs URL-Safe Base64 encoding on the hash, using the result as the code_challenge.
The third-party application uses the code_challenge to initiate an authorization login request to Zhuyun IDaaS. After the user logs in to Zhuyun IDaas, Zhuyun IDaaS will redirect back to the third-party application, carrying the authorization code parameter.
The third-party application uses the authorization code and the code_verifier to call the Zhuyun IDaaS API interface to exchange for an access_token.
The third-party application uses the access_token (valid and not expired) to call the Zhuyun IDaaS API interface to obtain user information.
# Development Steps
The Zhuyun IDaaS platform adopts the OAuth 2.0 PKCE Authorization Code Grant mode for integration. The development flow is as follows:
# Step1: Obtain PKCE Authorization Code
Click to view the interface for obtaining PKCE authorization code
# Step2: Obtain PKCE Access Token
Click to view the interface for obtaining PKCE Access Token
