Overview
# Introduction to OIDC
OIDC (OpenID Connect) is an identity layer built on top of OAuth2 and is a standard identity authentication protocol based on the OAuth2 protocol. It enables clients to verify the identity of end-users based on authentication by the authorization server. OAuth2.0 provides authorization, which is the process of verifying whether there is permission to access certain content based on rights. OIDC provides authentication, which is the process of verifying identity.
OAuth2 uses access tokens to authorize third-party applications to access protected information. OIDC follows the OAuth2 protocol flow and, on this basis, provides id tokens to solve the user identity authentication problem for third-party applications. OIDC delivers user identity authentication information to third-party applications in the form of id tokens. The id token is encapsulated based on JWT (JSON Web Token) and features self-containment, compactness, and tamper resistance. After verifying the correctness of the id token, the third-party application can further read more user information using the access token obtained through the OAuth2 authorization flow. To understand the id token, let's first look at what JWT is.
# Introduction to JWT
# What is JWT
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. Since this information is digitally signed, it can be verified and trusted. JWT can be signed and encrypted using a secret (with the HMAC algorithm) or a public/private key pair using RSA or ECDSA.
Digitally signed JWTs can guarantee the non-repudiation, authentication, and integrity of the id_token, but they cannot guarantee its confidentiality. Therefore, it is not recommended to include sensitive data with confidentiality requirements in the id_token.
# What is the structure of JWT
JSON Web Token consists of three parts in a compact form, separated by dots (.), which are: Header.Payload.Signature
# What is an ID Token
An ID Token is a security token, a JWT containing specific claims. Specific claims refer to information produced by the identity authentication server when verifying the end-user for use by the client, such as issuer (issuer), end-user identifier (sub), client id (aud), expiration time (exp), token issuance time (iat), etc. It can also include other claims. The ID Token is issued by the identity authentication server (OP) and handed over to the client (RP) for verification. It looks like this:
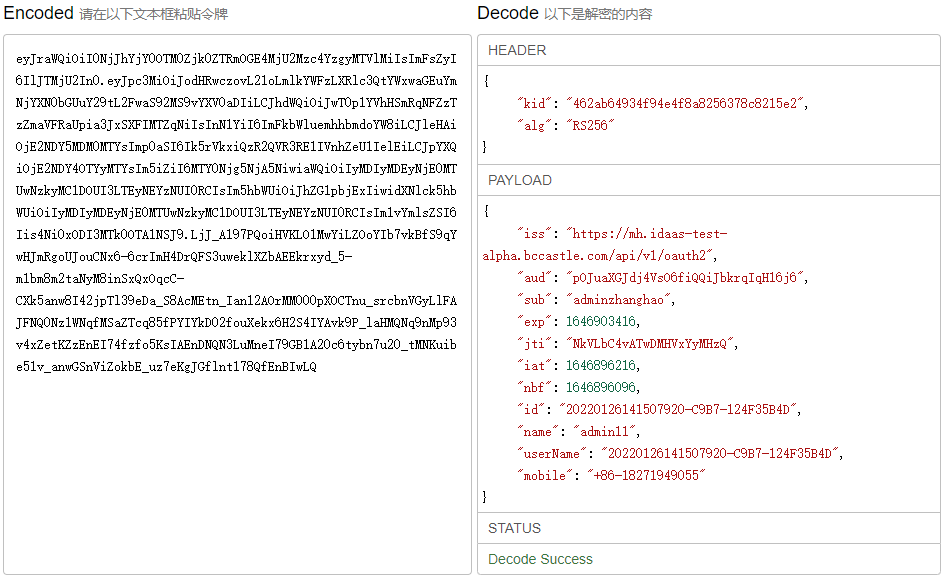
# Main Components of the ID Token
The ID Token mainly contains the following mandatory claims, and custom claims can also be added according to application mapping configuration.
iss = Issuer Identifier: Mandatory. The unique identifier of the entity providing authentication information. Fixed as: https://{your_domain}/api/v1/oauth2.
jti = JWT ID: Mandatory. A unique identifier for the token, which can be used to prevent token reuse.
sub = Subject Identifier: Mandatory. The account name of the application. The identifier of the EU provided by the iss, unique within the scope of the iss. It is used by the RP to identify the unique user. Maximum length is 255 ASCII characters.
aud = Audience(s): Mandatory. Identifies the audience(s) for the ID Token. The clientid assigned to the third-party application after application access is granted.
exp = Expiration time: Mandatory. The expiration time. ID Tokens beyond this time will become invalid and will no longer pass verification.
iat = Issued At Time: Mandatory. The time the JWT was constructed.
nbf = Not Before: Mandatory. The initial generation time of the JWT. ID Tokens with a time before this will not pass verification.
# Terminology
Bamboo Cloud IDaaS Unified Authentication Center: That is, the authorization server, hereinafter referred to as Bamboo Cloud IDaaS.
User Center: A portal system provided by Bamboo Cloud IDaaS for enterprise users to centrally access third-party applications.
EU: End User: A human user.
RP: Relying Party, used to refer to the trusted client in OIDC, the consumer of identity authentication and authorization information.
OP: OpenID Provider, a service capable of providing EU authentication (such as the authorization service in OIDC), used to provide EU identity authentication information to the RP.
UserInfo Endpoint: User information endpoint (protected by OIDC). When accessed by the RP using an Access Token, it returns information about the authorized user. This endpoint must use HTTPS.
ID Token: Data in JWT format, containing EU identity authentication information.
